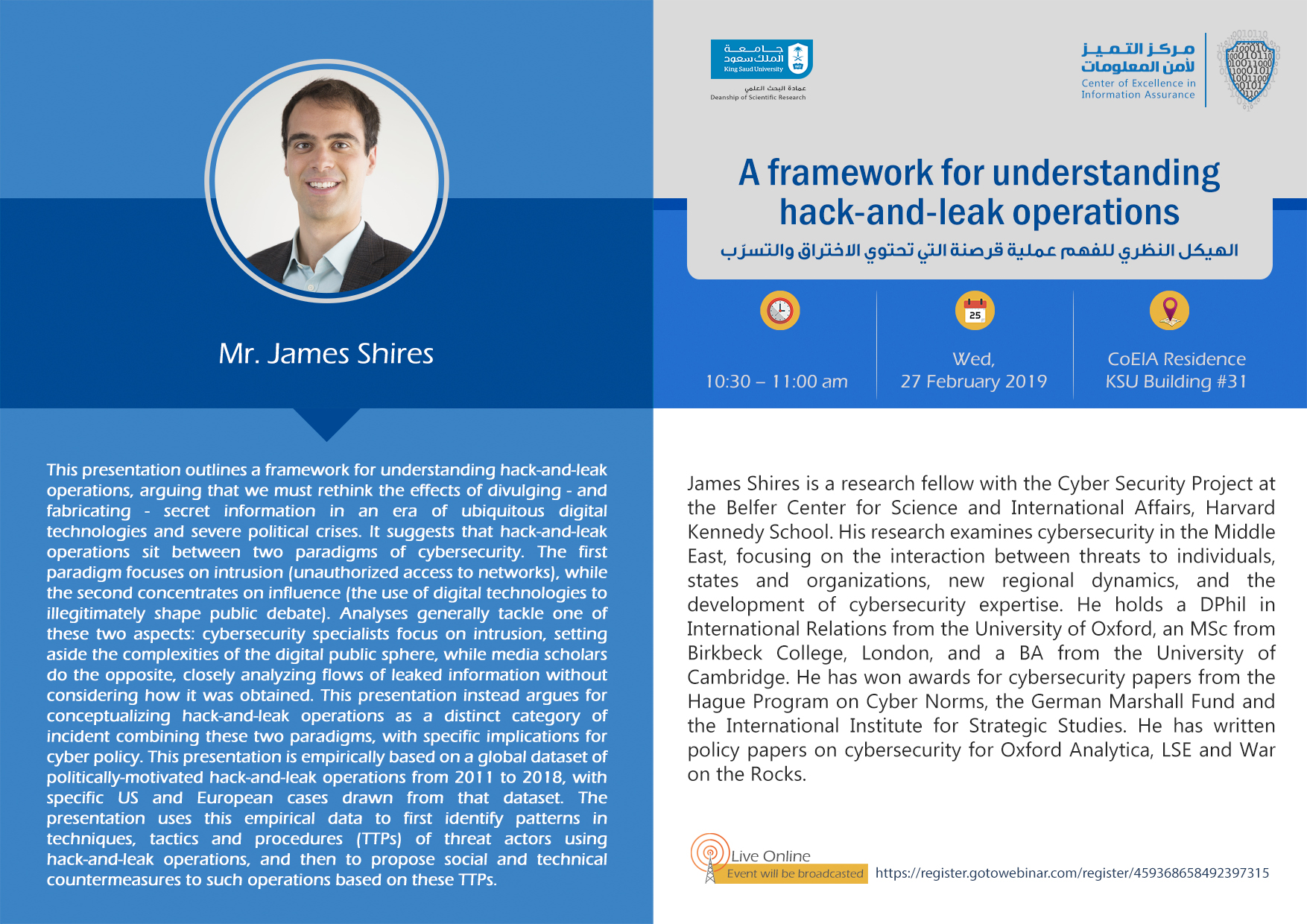
This presentation outlines a framework for understanding hack-and-leak operations, arguing that we must rethink the effects of divulging - and fabricating - secret information in an era of ubiquitous digital technologies and severe political crises. It suggests that hack-and-leak operations sit between two paradigms of cybersecurity. The first paradigm focuses on intrusion (unauthorized access to networks), while the second concentrates on influence (the use of digital technologies to illegitimately shape public debate). Analyses generally tackle one of these two aspects: cybersecurity specialists focus on intrusion, setting aside the complexities of the digital public sphere, while media scholars do the opposite, closely analyzing flows of leaked information without considering how it was obtained. This presentation instead argues for conceptualizing hack-and-leak operations as a distinct category of incident combining these two paradigms, with specific implications for cyber policy.